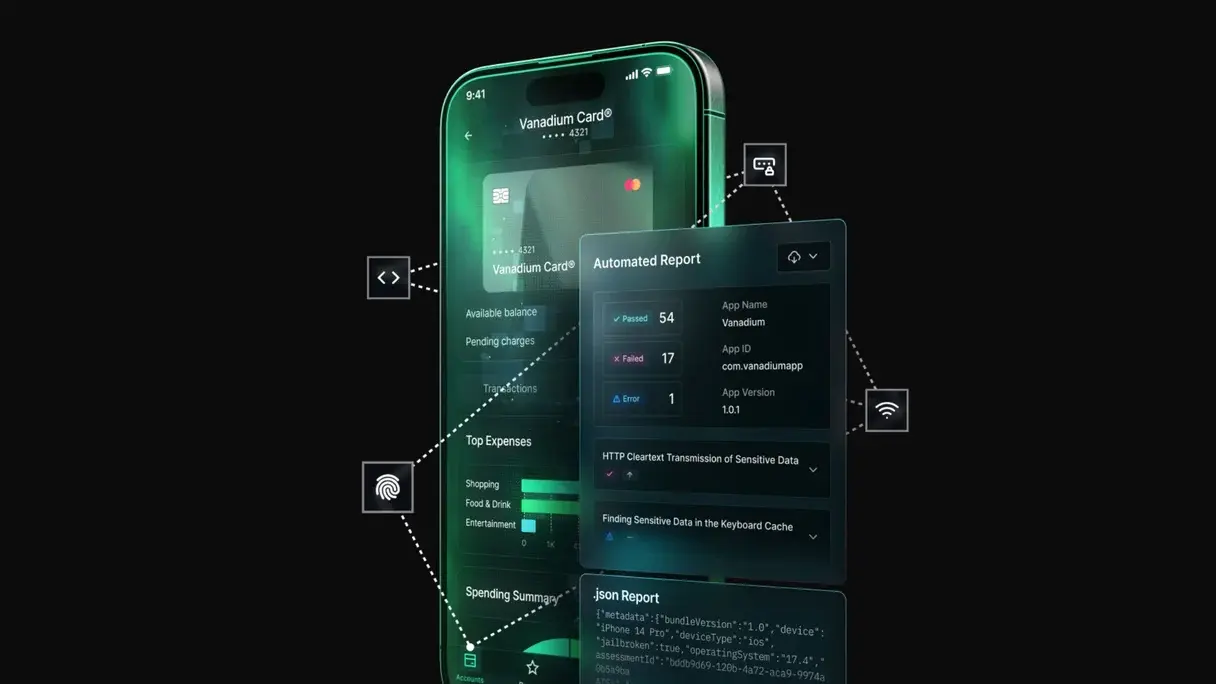
Identify Mobile Attack Surfaces
Analyze the mobile application architecture, APIs, and communication channels to map potential entry points.
Analyze the mobile application architecture, APIs, and communication channels to map potential entry points.
Assess weaknesses in authentication, data storage, encryption, and application logic.
Deliver actionable recommendations to strengthen mobile application security and protect user data.